Cloud and Container Security Webinar from Runecast
Watch our latest webinar to see how Runecast enables even greater depth of scanning in cloud and container security. You’ll see our Product Marketing Specialist Steve Salisbury talk through the old approach to cloud & container security and then how Runecast are offering you a new way, shifting left towards DevSecOps and great efficiency. He’ll also cover a few of the latest updates in Runecast 6.2 and the essential integrations that are making your life easier.
There’s also a live demonstration from our Solutions Engineer Steve Bettison showing how Runecast works for Google Cloud Platform and Head of Product Management Markus Strauss demos the new admissions controller functionality for containerized workloads.
Transcript
Steve Salisbury
Welcome to this Runecast insight into achieving complete compliance in cloud and containerized workloads with Runecast. My name is Steven Salisbury and I'm a product marketing specialist for Runecast and I'm joined today by two others from Runecast. So I also have with me Steve as advertised and guest speaker. So Steve, would you like to introduce yourself?
Steve Bettison
Yeah, good afternoon, everybody, and a warm welcome to you all. My name is Steve Bettison. I'm one of the solution engineers at Runecast. And you're going to be hearing from me a little bit more later on when we run through the demo of the new features.
And surprise guest speaker would you like to introduce yourself, please?
Markus Strauss
Of course. Thanks, Steve. Yeah, my name is Markus Strauss. I'm the Head of Product Management at Runecast. And first of all, thanks. Thanks, everyone, for taking the time and I will have a very, very small part later on in the discussion, where we talk a little bit more about some of the work that we've been doing around Kubernetes and image scanning capabilities. But great to be here.
Steve Salisbury
Thanks, Markus. Okay, so before we kick off, and we have a look at what's new with version 6.2 of Runecast, I have to say I'm really excited to be showing you this today. But let's just for those of you who've joined us who don't actually know, because we understand that some of you are new to Runecast. So if you don't really know what Runecast is about, let's just have a brief overview of that. So as we can see here, it's an AI driven platform. So it it works for us across many different aspects of our environments for vulnerability management, security, compliance, and, you know, it's a platform basically, which can deal with our on prem or our cloud. And that's covering, you know, our VMware our Kubernetes, digging into those VMware, config KBs and best practices across the board. So it really is designed as a platform, which can be used as, you know, one single point of view for absolutely every single environment that you have.
So let's have a look at what's new in Runecast 6.2. So we've added Google Cloud Platform. So this is really exciting. We'll have a little look at that in a bit. We've also as Markus was saying, we've introduced some new new areas around Kubernetes, and security and image and container scanning. And we'll have a little look as well at IT operations management integrations that we've brought in and some usability improvements. And I'm just going to talk you through those. And Steve's going to actually do that live demo for you at the end. So we can actually see this in real time and fully understand what this means for us. So let's dig in and have a look at Google Cloud Platform workloads, and you know, just have a bit of a discussion around that area to see you know, what's really going on. And when we think about what's happening in the world, in everyone's environment at the moment. So a lot of people will have on premise, and they want to start migrating to the cloud or they already have started or migrated to the cloud. So you know, cloud adoption is becoming increasingly popular. And there are a lot of hybrid environments out there. As I was saying, the Runecast platform enables us to actually see what's going on in the cloud and on premise both at the same time. So it's really powerful in that and it brings us that single source of truth.
So Runecast started off in the cloud, with AWS. And then we brought in Azure monitoring, and now we're proud to tell you that we have Google Cloud Platform monitoring as well. So Runecast now stands firmly as a cloud native application protection platform. And we're really proud of this and this is an amazing release and it's really brought some great insights that are gonna really help you out in your environments. But what does it mean when we start looking at the cloud? So with all cloud providers, they're duty bound to secure the underlying infrastructure they provide, but they don't provide solutions for you to monitor your overlying deployments. So whatever you put in the cloud is your responsibility to secure and Runecast, as I was saying, provides that single source of truth that we need to ensure our cloud workloads conform to best practice and are protected from vulnerabilities and conform to security compliance requirements as well. So I'm not going to dig right into what we've got for GCP at the moment, Steve's going to be showing you that a bit later on, so I don't want to spoil his demo. But Steve, as we move on, and we start to have a look at you know, Kubernetes and what's going on there. Do we have any questions coming up at the moment?
Steve Bettison
No questions so far Steve.
Steve Salisbury
Okay. So as I was saying earlier on, and I'm sorry I forgot to repeat myself when we started off, if you guys do have any questions at all, we do have the q&a section. So please feel free as we're going through to pop them in there, and we'll answer your questions for you. So Kubernetes management. So until now Runecast has provided checks on cluster roles, cluster bindings, nodes, names and spaces, and pods. And in 6.2, we've now included container image scanning, which allows us to go deeper and check into application vulnerabilities in containers. So obviously, this enables Runecast users to gain further vulnerability and security compliance. But it also allows you to take a shift left approach to Container deployment. And we're going to have a little look at that in a second just to explain it a bit.
So for those of you out there who are not sure what the shift left approach is, just so that you can get a great idea about how that works and how that's gonna work for you. So with Kubernetes management, we have four stages to releasing containers into production. So we have our planning, design, develop, test, and then we're going to deploy it into our production site. So the problem with this traditional release model is that when we get to deploying into production, we're releasing unsecure containers which leave our workloads open to attack. So you know, once again just to repeat that, we're going through the plan and design, we're developing and building, we're testing putting that in a test environment to make sure it's good to release and then we deploy and release that out into production. So it's only at that stage when we've deployed into production that we start to monitor and analyse for vulnerabilities, and this can already be too late. So what we need to do is we need to take this shift left approach. So we need to take, as Steve will show you in the demo, this shift left approach by using Runecast, we can actually monitor and analyse our container images against three levels of admissions, but what is the shift left approach?
So as with the traditional approach, we're going to plan and design, we're going to develop and build and then we're going to monitor and analyse. But what we want to do is actually stop there with the monitor and analyse. So sorry, I said as with the traditional model, but yeah, we plan and design, we develop and build, but now we're monitoring and analysing. So what this means in real time is that I can actually check and we can use Runecast for this. We can check our container images, make sure that they're actually secure before we actually put them out to our test environment.
So this is really important. You know, we can monitor and analyse our container images against three levels of admissions policies before we release them for testing. And in real terms, what this means is that we're not putting anything that's exposed into our production environment. So we know we've checked against the latest vulnerabilities and we're not firefighting anymore because when we come to deploy and release, and then we're on to monitor and analyse because it's already out there in production, the way that Runecast works with our weekly updates means that any new vulnerabilities that are put out there, we're going to be monitoring for but we already know that we've secured those containers.
So we're not actually looking for anything, post deployment. What we're doing is we're checking any new vulnerabilities that come out. So this makes your team really proactive in the work that they can do. And they're not firefighting, so we haven't put something out there that we need to be checking from the start. We've already secured that. And now we can just check for those new vulnerabilities that have come out and our team is proactive. So hopefully that explains to you this shift left approach. We're going to explain that a little bit more, you know, Steve and Markus are going to help us out with understanding that a little bit more a bit later on in the live demo. And before we jump into our item integrations and usability improvements, Steve, do we have sorry, I can't see at the moment but do we have any questions that have popped up at the moment or…
Steve Bettison
No, still the same situation, no questions have appeared so far.
Steve Salisbury
Okay. And please, everyone, you know, feel free to pitch your questions in. Okay, so what's new with ITOM integrations and usability improvements? So, the first thing that I'd like to discuss here is open ID connect. So for those of you who are not sure what that means, it means simpler integration for your team. So Open ID Connect is when for example, you have your Google account at work, but that allows you to also enter different aspects of your work. So for example, if you're logging into JIRA and Confluence, it will ask you to log in do you want to log in using your Google account. So we use this every day without even realising what we're using maybe.
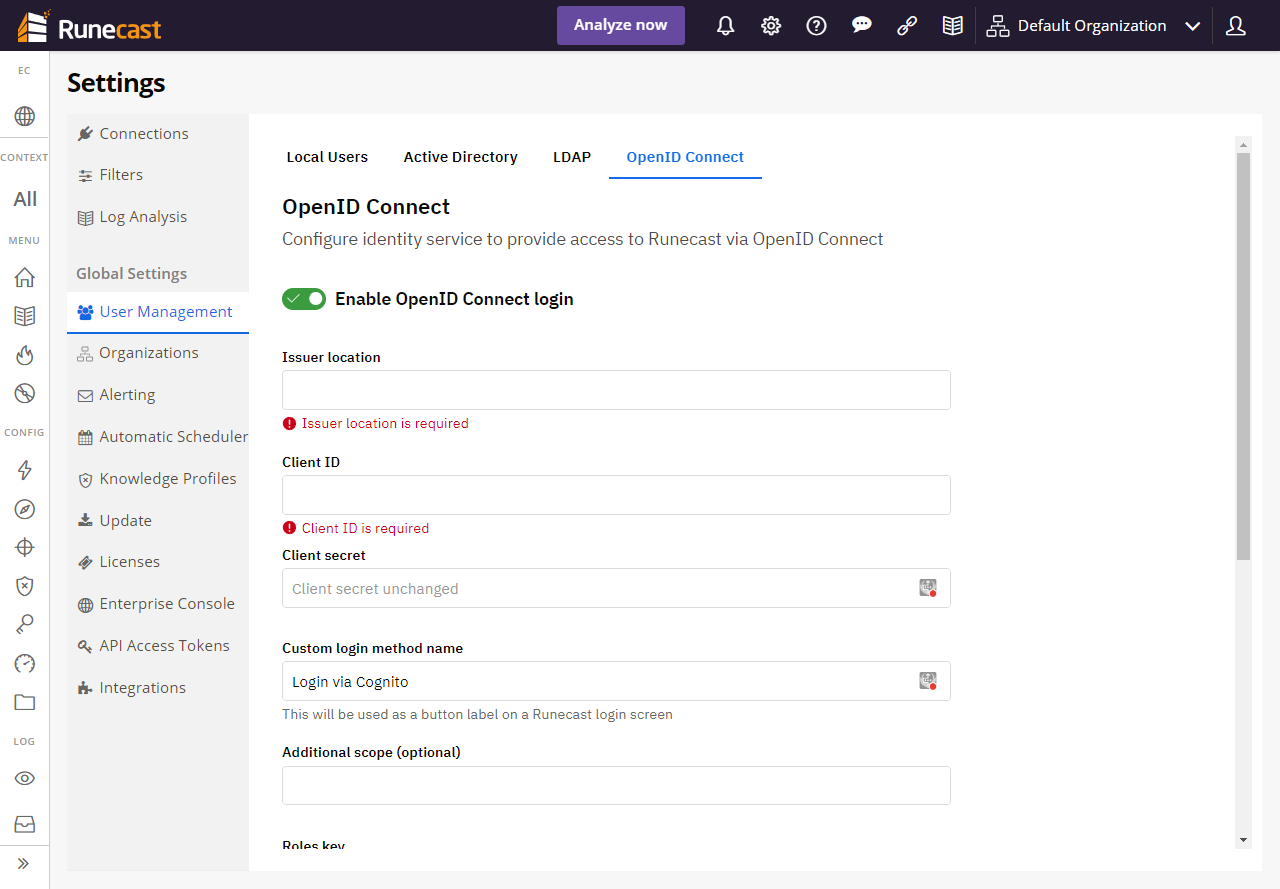
So just to understand Open ID connect, and how that works. You know, that's going to make your life a lot easier for integrating with Runecast. And that means that you know, especially if you've got a smaller team, and you're not using Active Directory or something like that, you don't need to set up individual user accounts. We can use Open ID connect and connect straight in for our users.
So we also now have JIRA Service Management integration. JIRA Service Manager is a ticketing system. So we started off with ServiceNow. But now we have integration with JIRA Service Management. So if you're using that, that's going to be really helpful for you. You can actually send the tickets directly from Runecast to JIRA Service Management, and set up your tickets for your administrators.
We've also introduced the not analysed issue state. So what this is doing for us is, it might be that you don't scan every single day. It might be that you run a scan once a week because you have a small team, or maybe you just don't have so much to stay on top of and you don't necessarily need to keep scanning so much. But what happens when we release a new knowledge definition? You don't know that we've released that and there could be some issues and vulnerabilities that we've included, that you now don't know about. You don't know that you need to go and check against them. So when you come into Runecast, it's going to tell you with the not analysed state that actually it's a good idea to run a scan now because you need to analyse against these issues. So that's a nice, another little touch and you know, something which is trying to keep you informed so that you can stay on top of your environment.
We have new performance and usability improvements and so Steve's going to show you the usability improvements when he runs his demo. And you know the performance for Runecast, we've really stepped it up and made sure that everything's running super, super smooth. So that's another great thing that's been introduced for this release.
So before I do death by PowerPoint on you, I just have one last slide for you guys. So we've also released some new security compliance, so DISA STIG for VMware vSphere seven. We've also got STIGS for Linux RHEL eight, which we introduced before this release, but I just wanted to make sure that everyone is aware of it, because it came out just before this released NIST profiles for Azure and we've got the BSI profile for Windows OS as well. And obviously, you know, we do release new vulnerabilities best practices once a week, but with this release, we introduced 26 New Linux vulnerabilities and the critical MS vulnerability that you can see there at the bottom.
So that's my death by PowerPoint for you. And I hope that that was informative for you, and it's given you a nice overview. I'm going to hand over now to Steve. So Steve, do we have any questions coming up at the moment or…
Steve Bettison
No, still no questions at the moment.
Steve Salisbury
Okay, and as we were saying earlier on, you know, please feel free to throw those questions in there. So, Steve, if you'd like to take control, I shall hand over to you for the live demo.
Steve Bettison
Great. Thank you very much, Steve, for introducing those new exciting features in Runecast version 6.2 and their importance and value that they bring to both new and existing customers. So let's get into the demo of Runecast analyzer and show off these features. So let me just share my screen. Okay, before we get into the new features, I'd imagine there'd be a few folks on the webinar that may not have seen the user interface for Runecast. There'll be many of you that will recognise this the user interface of what we're looking here just to put a bit of context around this before we dig in to looking at Google Cloud Platform coverage.
This is the main dashboard for Runecast analyser and we are analysing across all the different systems here. We're showing configuration issues by severity across all of those platforms. We're looking at best practices adoption vulnerabilities detected. We've got some knowledge base articles there, this relates to the VMware environment. And we break this down by configuration issues by layer. So just to run through the systems that we cover, VMware, a couple of VCentres there, VMware Horizon, we've got an NSX T manager connection there. VMware Cloud director Kubernetes, which we're going to dig into a little later on for container image scanning, which Steve has already covered. We'll have a look at that. And even operating systems as well as Linux and Windows devices but you can see here we have a Steve already mentioned we have AWS as one of our coverage for cloud. We also have Microsoft Azure and now exciting that we've released and now got Google Cloud Platform.
So we're going to dig into that now. So I'm going to click on that one and the dashboard will change to look something like this.

Now this dashboard very much aligns with what you would see for Azure and AWS so again, we are breaking down the issues by severity here. We've got that best practice adoption. It's a fairly new environment for me so not much going on here. This will obviously grow in time and things will change. We want to get that best practice adoption up to 100%. And then we've got configuration issues by layer. So we're breaking that down into management, virtual machines, compute, network and storage. And these are the profiles that we're analysing against. And you can see there the number of issues and objects.

So what we're covering for Google Cloud Platform is Google Cloud Platform, general best practices, and the CIS security compliance framework. And you see at the bottom here, we have a history of findings. This will grow over time. But we do have the ability sort of slider bars here as standard so that we can zoom in on points of interest there to see where perhaps things have changed over time. So if we come back to the main menu, these are configured so for configuration analysis we've got best practice, security compliance, and we're also going to look at the configuration vault as well where we can see baseline comparisons with different objects within Google Cloud. And also look at configuration drift.
We have an inventory view here. Just briefly show you this. This is a breakdown of those objects in issues. I can simply click on the VM instances here and this gives me a list of the CIS security compliance framework objects and general best practices as well as we've got some majors there. So that's one way of looking at it. We've got an all issues view as well where you can see everything from a bird's eye view. We have the ease and the ability to look with the filtering tools, options at the top here. We can go back in time, we can look at different aspects of this. Now what has changed here, we've now got this percentage bar.
So before we used to show objects that were passing, and objects that were failing, passing with green failing with red and then an overall status. Now, again, with our environment. In order for something to pass, it has to have all of the objects passing having a passing status to get that overall status of passed, that you can hover over each of these and it'll tell you how many objects you've got one failing there, as I scroll down, we can see that there's a split there. You know, some of them might have 20 objects, and it will show the split there to get to an overall pass you would need to have all of those objects passing.
Let's get into the best practices. So I'm going to just pick one, we'll look at an example. And this is just to highlight the simplicity and ease and use of a Runecast analyzer. So we've identified these best practices and we've got certain things that are failing certain things that are passing. Well look at this one here. We've got a couple of Cloud SQL databases that should not have a public IP address. So single click, and we have all this information at our fingertips. So the description there that we just outlined, we have the remediation steps. So this is using the Google Cloud Console and what we need to do there. We've also got some information about the command line that we can use as well. There's also some notes under section and some references. If we go across to the right hand side, again, this is all very familiar; this is standard throughout Runecast Analyser. The solution we have the issues details there, but we can have a look if we wanted to, at the issue ID and we can go to the original sources. So all of that information is there.
So the name of the game obviously with best practices, we want to obviously with our Google Cloud Platform, and any of our other platforms is to, to follow that best practice adoption and get that level as high as we can. So turning these two objects to green. What are those objects? We can go to the analysis findings here, and in here, this is showing my two SQL databases there and there you go we've got these public IP addresses that we need to change in order to follow that best practice guideline. If we now dig into the security compliance, so for Google Cloud, we have the CIS framework. Again, very much the same look and feel with this. This percentage bar is now common throughout all of the functionality and platforms within Runecast analyzer. We've got 81 issues here. And I'm just going to click on one.
Let's look at this, ensure cloud DNS logging is enabled for all VPC networks. So again, single click, if we go, we get the description, the rationale, all of the information that we need at our fingertips, to be able to go in and modify this so that we can be compliant against this particular thing. This particular item, again, our analysis findings there, there is our device, cloud DNS logging, it's not configured. Again, the objective of this is to get as you know, as compliant as possible. So, you know, we're turning these objects into green and getting an overall status of passed. We also as standard are able to export, you know if you've got auditors in and you need to prove that your Google Cloud Platform is compliant. And you've got auditors in, we've got the ability here to export out to a CSV format or a PDF.
Let's go into the configuration vaults. And I'm gonna, I'm gonna just change across to another environment that I've got because I have more information in this other environment for baseline and historical changes. I've just flipped over. Now this is all new up at the top here, this configuration vault menu here so we've got this inspector baseline comparison and historical changes.

And we are able to look at view different objects within here. So the default here is looking at VM instances. And I'm going to probably stick with that for the purposes of the demo. But we can go and look at cloud storage buckets, DNS policies, firewalls, SQL instances and so forth. And I got, you know, the overall status of what's going on. I've only got two VMs here, but imagine I've got 50 or 100 VMs. I can see what overall status is. I've got one running one terminated here, machine types here, and perhaps what zones they're in.
And, you know, I can then from this inspector, if I want to do a baseline comparison, perhaps with my running machine, my running VM to the terminated one, I can click on these two blue arrows here and it's telling me there are three changes. So I can click in there and have a look at the changes. Now one of the obvious ones, of course, is we've got a status: one that's running and one that's terminated. That's pretty obvious, but this information here, the CPU platform is different. And the disk count is different. So if you've got a gold image in there and you want to, you know, compare and do baseline comparisons, this is a very, very powerful tool, the configuration vault baseline comparison. This is where you come to look at where you can see changes that have occurred within your environment.
And finally, on this bit, the historical changes. If I click on that, what this allows me to do, and again as your environment, your analysis, you're doing that maybe daily or every two or three days, you're building up a history. What we're able to do is a baseline analysis, I can go back, we can select the latest analysis here and we could go back in time. Not gonna have to go back too far in this particular lab. Click Apply to run VM instances here, and I can see what's changed. There's only one particular change here. And I believe it's the disk count. Yes, it is. So this is just highlighting that in that period of time. We've added some disks to that running machine there. Now if we'd have added more virtual machines into our Google Cloud Platform, we would see something on this bar here to say that, you know, X amount of objects have been added X amount of virtual machines have been added to that.
So that's the power of the configuration vault to be able to come in and inspect, come in and do baseline comparisons, and to look at historical changes. So the key benefits of Google the Google Cloud Platform, customers are now able to analyse their workloads, irrespective of which CSP, they're utilising as is we're now covering the you know, the big three in AWS Azure and now GCP. So this is going to help our customers with their configuration and security posture management no matter what the CSP is. It's also very much I hope you've seen it's a proactive approach to analysing GCP against best practices, and of course, that CIS compliance framework.
Customers will also have greater visibility into how their environment is configured at any given time, as we've just seen as we've just run through being able to do baseline comparisons, and historical changes. But not only that, adding GCP to Runecast really does enhance our solution as a complete CNAPP solution for multi cloud and hybrid cloud. environments. I'm gonna take a little breather there. Steve, have there been any questions that may have popped up?
Steve Salisbury
No, we don't have any currently. Unfortunately, please feel free to put your questions in the chat.
Steve Bettison
Yeah, please do put any questions, please, please drop them in the chat window. Okay, let's move on to the next exciting feature that I want to cover which is the Kubernetes container image scanning.
So before I would dig into that, I just went back to the main dashboard. Now you can see here, under the main menu, we've got image scanning. Now, this will only appear if you are connected to a Kubernetes platform. So if you're connected Runecast analyzer to a Kubernetes environment. If you haven't got that in your environment, image scanning will not appear here. So what I'm going to do is drop into the Kubernetes dashboard. And as before what we were able to do is best practices, best practices adoption, security, compliance and do vulnerability management against clusters, nodes and pods. With this image scanning where this functionality will allow our users now to find vulnerabilities that are not strictly Kubernetes related, but are present in the container images that are used in their infrastructure.

So essentially, it's checking the application packages inside the container image for vulnerabilities. So that shift left approach that Steve was mentioning earlier. So if I dig into the image scanning now what we have here is a list of images that have been scanned over the last few days, few weeks. They've been, the trigger type has been a manual scan, and we'll get into a little bit more detail about other types of scanning when I bring in a Markus but effectively we've got admission policies. So what those do effectively, this is specifying the level of exposure that is permissible for perhaps a new workload, you know, as part of a development pipeline, you know, to allow customers to include in their image scanning, so we have three of those.
I'm not going to go into too much detail but policy ID one might be perhaps used for a test environment. It's looking, it's compliant, it will it'll run against that and it will say it's compliant if there are no critical vulnerabilities detected you perhaps might use policy ID two for a pre production environment where we're looking at, you know, there's no critical or high severity vulnerabilities discovered for which there is a fix available, and then perhaps your production environment, the most restrictive there would be using policy ID three where we're, you know, it's critical high and medium severity vulnerabilities discovered, which you know, there is a fix available.
So, we've got some history going on here. We've been running this Jenkins one, this Alpine image as well. If I just dig into this particular one here with no critical vulnerabilities that was run a couple of days ago. What does it look like? It gives us a list of the vulnerabilities. And as you can see, we have what we're getting to here is we're actually showing you where we can find the fixed version that's going to resolve this. So if I was looking at this and I needed to get the critical ones resolved, I'd be looking at, you know, with these particular packages that we're talking about here, the package name, I'd be looking to get that fixed version installed, and where that where there are perhaps critical ones here that there aren't a fixed version, then maybe you'd be looking at a different container image.
How do we scan from a manual basis? We can go in and click on the scan image here. I can select the image that I want to scan and I can select my policy here. I'm going to click then there are no critical vulnerabilities, click the Scan. And it's coming back with a similar result that I had yesterday, but it's different from ones that I did two days before so obviously those packages have been updated. And again, if we click in that, let's just click back in here. If I want more details on that particular one, I can simply click on that single click and it's giving me a little bit more information here and the description and the CVEs score in there.
Now we talked about doing manual scans, I think I'm just going to introduce Markus into the conversation around API's and how we can link this to software like Jenkins for that shift left approach and you know, shift left pipeline so Marcus if you if you would like to join here.
Markus Strauss
Thanks. Steve has already given us different ways of looking at the scanning of Kubernetes images right. The manual scan, we just discussed the other being driven by Kubernetes own admissions controller, Kubernetes has a built in admissions policy controller if you will, that can be triggered as part of the deployment of a containerized workload. Then do various things and by various things I mean, also, different policies can be set. But this is also extremely helpful for anything that's related to the security of the actual container itself. So as part of our general image scanning capabilities, we've also introduced a way an API does go in at a specific time that will directly speak to the admissions controller so to speak.
You know, you can see here in my development environment, we have a few more trigger types available than what was seen in the demo environment just before. So the Kubernetes submissions controller effectively, we can attach to shift left conversation in the sense that it allows you to effectively attach Kubernetes image scanning from Runecast into your deployment process, right. So this is a webhook integration. It can be very quickly adjusted to your deployment process and you can trigger the same policies, as Steve has shown earlier on, which are these three types of policies and you can think of them a little bit like okay, this policy one is probably the least restrictive.
You can think that this is where I deploy into my test environment, because there isn't really any critical workload or any data that could potentially have a problem. Policy two might be your staging or pre prod environment, because that deployment policy is already a little stricter. And then policy three really is well, that's the most restrictive, right and you would want to use that, let's say for your production environment deployments and things like that.
The inherent benefit of Kubernetes being it is very easily and quickly deployed and generally, you know, what you would call probably, world workloads, they don't live very long. They can be spun up for specific tasks, then destroyed again, meaning really, for you to be secure and to have the ability to do vulnerability assessment. It has to be part of the actual deployment process, unlike with potentially more traditional workloads where there's there's a lot more time where this workload exists, where you can instal something you can do the vulnerability assessment, do the mobility management and the scanning and then how they resolve that you can act on images by their very nature are closed up systems. And very often don't live very long.
So this whole process of scanning vulnerabilities has to become part of the deployment process. And that's, in essence, where the shift left conversation really came from. It was shifting the security aspect further to the left, i.e. further to the development process, rather than after the development is done. And I can see we have a hand raised. So let's have a look at if you have a question, please put it into the q&a.
Steve Salisbury
So we have a question here about how AI is effective in the shift left approach.
Markus Strauss
Yeah, it's a good question. And generally, from my perspective, a lot of the way we get to the information, because you have to understand obviously, any any sort of security standard, any sort of CVE all of these things are effectively human readable pieces of information.
And AI in this particular instance, means our backend is a natural language processing driven back end takes all of that human readable knowledge, all of these different types of pieces of information, whether these are CVEs or whether these are compliance standard security standards, things like that, and then creates machine readable rules based on these. These machine readable rules, then feed into Runecast and allow customers to have a very pain free way of adding new checks and new rules and new things to look out for in an automated fashion right. It just makes the process for customers a lot easier. And I hope that that answers to a degree that question.
But let me just go back to the conversation around admission types right. So we've we've looked at these the covenanters admissions controller trigger is it's built in the name it's Kubernetes, right and it will only work obviously with the Kubernetes admissions controller and it's a it's a way to include the scanning that we look here in more bespoke deployment scenarios. But generally most of us are familiar with things like Jenkins, Jenkins, Azure DevOps, GitHub Actions, all of these build pipelines. That's generally what we use if we talk about pipelines and build, right.
So what we've also done is we've created another API endpoint to be integrated into the likes of Jenkins. Right? To really become part of your development lifecycle, right? Again, thinking shift left, meaning we've got to move the security aspect or workload much further to the left, and allow that to become part of our development and deployment process. Right. So I'm using here an internal check to say, I'm going to build with parameters. So let me grab an image that we would want to deploy. Let's do this. So we'll have a look. We want Maria DB and Nginx. We can let's say we're going to start with policy one and we hit build right.
So what happens now is that this is part of the build process, right? So this is part of the development of my team running a build for something new that I want to release right. But unlike the traditional ways of doing image scanning, where there is a degree of manual steps involved, this is fully automated in the sense that Jenkins has now already sent the image to Runecast and if I go back into my development instance here, and I do a quick refresh.
Now mind you, this is a development environment, so it might be a little bit slow, but you can see here we've got MariaDB and Nginx. The trigger type was an API, we can see the policy was not compliant. Now if I go back into Jenkins, I can also now look in Jenkins directly and I can see what happened here status. I can have a look at the logs and see that this has not passed and obviously there is a very nice red. Now if we do that again. We build one where we use the same one and now we'll do a less strict policy or let's even do yeah, let's try this one. This should work. Let's see if that works. As he says he doesn't know whether it will work but we know this one passed.
Now the beauty of this from a DevOps perspective or DevSecOps perspective is the fact that it doesn't mean that your development teams have to do anything different than before. There are no different steps involved for the development teams to do anything extra or anything in addition in order to ensure that your containerized workloads get deployed, whether that's into test, pre prod staging, or any other environment, anything you build automatically goes through.
Any image and you know this, I think this is really, really important to note, while the Kubernetes admissions controller is, like I said earlier on by its very name Kubernetes specific, this is containerized workloads. So that means that can be your direct Docker. It could be a different orchestration to Kubernetes. So anything containerized image can be used here and you can effectively integrate your entire DevOps or your entire development lifecycle into your security lifecycle. And ensure that workload stuck ployed you, the processes are secure and free of known vulnerabilities right. And it really helps with things like, you know, your attack surface when it comes to anything that's part of the build process.
Anything that's part of the development process, without requiring your developers to actually do anything more or take any additional steps. So that was me with a very quick update on that. And I know we're getting short on time as well. So I think Steve Bettison, if you want to take over and continue.
Steve Bettison
Yeah, thanks very much for that Markus.
Markus Strauss
No problem.
Steve Bettison
In terms of what we've covered, look at the percentage bar thing in the displays that's changed in this all issues view here. This is something that's new, we've already covered. But you also mentioned about the not analysed state. So when Runecast analyzer when we bring out new compliance rules, or perhaps there are new vulnerabilities that are going into your system and you haven't had to scan your environment for a few days or maybe even a week.
What you will see, just flip over to the other side, is you'll see this kind of status and you're able to search using the filter bars here, which is what I've done already, while Markus was talking and this is identifying these vulnerabilities that are in the system, but they haven't been analysed yet. So what you would need to do there is run an analysis and depending on what it finds it may find that you are compliant or you're not vulnerable on that particular vulnerability or it might identify objects that you are vulnerable to. So quite a neat, useful feature. I think it's going to be a real benefit to our customers.
The other things that I want to just cover very briefly ,and Steve has already mentioned these, if I go into settings, two things while we're talking about Google Cloud and Kubernetes just to show you how simple it is to set up with Runecast analyzer how to connect with Google Cloud Platform connection, we just simply click on that Add GCP and we need to just provide a service account key there.
You get your key, choose your key, select it and away we go. Once you've done that, you would then need to in order to get some results in your dashboard for your Google Cloud Platform you would need to analyse against that. If we come down here to Kubernetes. As you know, we've already got a cluster connected to a head node there. I can add another Kubernetes cluster if I want. And again, very, very straightforward. We just need that API address port number in that, SA token, click Continue and we connect and again once that's been connected, we then need to run that analysis in order to be able to see the results and you know see what's been discovered by Runecast.
If I then drop down to the knowledge profiles, and Steve has already covered this, you know we've added for the DISA STIG we've added VMware vSphere vSphere 7 coverage, as well as Linux RHEL 8. So there's a DISA STIG we've got vSphere and operating systems there. But version seven there for vSphere. NIST, we've added the profile added to that profile and we've added Azure as well. And this will continually, you know this is continually growing and the different compliance profiles are increasing across the different systems that we support.
And, you know, just to touch on what's you know, Steve mentioned that beginning we've added a lot of new vulnerabilities coverage for Linux, there's 26 new Linux vulnerabilities have gone in. And we've also extended the coverage for Windows Server OS as well. So some critical CVE have gone in for that as well. So I hope that's been informative. I hope that's been useful.
Thanks very much to Markus for jumping as well on the image scanning and really taking that into a lot more detail. Thanks, Steve as well, if there are any questions, Steve, we'd be happy to answer them. Other than that, I think you have one more slide just to cover if anybody wants to reach out to us and contact us and some addresses and things like that. I'll hand you back to Steve.
Steve Salisbury
Okay, so currently we have no open questions, unfortunately, but if anyone does have any open questions, we would definitely be interested to hear them. It's often the case that after you've watched a webinar, you then come up with some questions. So we're more than happy to answer them after the fact.
If you go to runecast.com/contact. What this will do is it will pass you on to the relevant territory manager of where you are and will be able to take care of you from there.
We had a question earlier on which I didn't bring up an answer live but it was, you know, what's the price of Runecast? So Runecast is subscription based. And again, please reach out. runecast.com/contact because depending on the size of your environment will depend on the price of Runecast. And we also have different billing aspects to the different technologies. So that's a very difficult one to answer in a very short space of time because obviously we'd need to know exactly what your environment entails.
Markus Strauss
I would also have oh, excuse me.
Steve Salisbury
Go ahead.
Markus Strauss
My one point I would also stress is for anyone on the call who's not already an existing Runecast customer. I will challenge you to go onto runecast.com you'll see up in the top right corner alink to download the trial.
Just download the trial literally, and I'm not lying, it takes 15 minutes to deploy Runecast. It's very, very straightforward, very easy, but again, gives you a much better idea of what you can do with Runecast. And it gives you an idea of how you can deploy it and how you can use it inside your own environment and get a very, very good feel for the benefit it can bring you.
Steve Bettison
There is one last question that's actually coming in. How do customers do compliance for all this without Runecast? It's a very good question. I answer that “with great difficulty”, I think because of what our solution does. And all of that information that goes into our AI engine to be able to analyse your systems could take in if you've tried to do that in a manual way, take you would take a team of people hours, days, weeks, months, it's you've got the information at your fingertips within cost analyzer because we've got that proactive approach. I don't know Steve, if you want to add or add anything to that or Markus.
Steve Salisbury
Yeah, I think that, you know, that's, it's a really good question. And, you know, traditionally you have that break-fix approach where something goes wrong, you try and figure out what that is. Then you're Googling it. Then you've got your answer and only now can you know, try and fix that issue.
So you don't have that single source of truth that Runecast is to provide you the information to say that this is going to happen in your environment. This is going to be an issue. Deal with it, and now it's you know, it's not going to be an issue.
So for something like, for example, VMware, it will tell you that you're going to get a purple screen of death, but you don't actually have that happening in your environment now, so I can look at that deal with the issue. And then I'm not going to get that Purple Screen of Death. I'm not going to get that downtime. And I've saved all of that time from you know, something going down trying to figure out what it is trying to Google that online. Because the information is right there at my fingertips and I can deal with it proactively before I have to firefight that.
Markus Strauss
Yeah, the one thing I would add to this is also the fact that I think in all of technology industries, we have always the habit of having a solution for a specific problem or technology. And every time you add a new solution or a new technology this is not a replacement, it's additive, right.
So for most of our customers, in a lot of ways, what we see is they start out with one type of environment, let's say VMware, and then there might be AWS. And then there might be some Azure deployments and then there might be some containerized workloads. And like I said earlier on monitoring and compliance aspects, they end up becoming additive. So you end up with one solution for VMware. One solution for AWS, one solution for maybe Azure and another one for Kubernetes and you end up with a team of people that needs to now deal with 3, 4, 5, 6 different solutions in order to solve one problem.
And what Runecast does is it brings all of these technologies together in one place in one platform, and allows you to have your team work with one platform and with one solution rather than with multiple different solutions. And it makes the whole process obviously a lot more streamlined, right because you don't have to train people on four different solutions anymore. It's one and there's obviously also some cost benefits to that as well.
That goes without saying so really what Runecast provides is the ability to bring all of these different tech stacks into one solution that allows you to do continuous compliance across your entire estate in one platform rather than having to use multiple different solutions.
Steve Salisbury
Thanks for that, Markus.
Steve Bettison
Yeah, well answered.
Steve Salisbury
So we're on top of the hour. We would like to thank you very much for attending this Runecast Insight again, I would urge you to please contact us at runecast.com/contact if you have any questions.
If you'd like to find out more about pricing about how you can get Runecast into your environment. Please feel free to contact us we're always willing to reach back to you and to have those conversations. So thank you very much, ladies and gentlemen, for joining us this afternoon. And thank you very much Steve and Markus for joining me in this Runecast insight webinar.

